Organization roles are available on the Pro plan and above. Some feature roles and capabilities require the Enterprise plan.
For granular, feature-by-feature restrictions (app allowlists, node denylists, concurrency limits), see Custom Roles. That is a separate, complementary system that restricts what organization roles grant. A user can hold multiple custom roles at the same time.
How it works
Union of permissions
A user with
{Member, Analytics} can do everything Member and Analytics allow. Revoking one role does not remove permissions granted by another.Member is implicit
Every org member automatically holds Member. It is not shown in the Manage Roles picker and cannot be removed without removing the user from the org.
Scopes are independent
Organization roles apply across the org. Team roles apply inside a single team. A user can be a Team Admin on one team and a Team Member on another.
Admin vs Feature roles
Admin roles (Admin, Manager) grant broad authority. Feature roles (Security, Developer, Analytics) grant scoped access to one area.
Organization Roles
Admin
Full control: billing, SSO, members, and every feature area.
Manager
Member operations, credentials, and analytics. No billing or security.
Member
Implicit baseline. Use agents, skills, flowbooks, and personal credentials.
Security
Custom roles, app policies, AI model access, and App Activity.
Developer
Hosted MCPs and Proxied MCPs. Requires Enterprise.
Analytics
Organization analytics, usage, and data export.
Admin
Role ID:
admin · Group: Admin · Scope: OrganizationCan access
- Billing, subscription, and credit limits
- SSO, SAML, and SCIM
- All member operations
- Organization credentials
- Team access and team settings
- Audit logs
- AI model access, app policies, custom roles
- Analytics, usage, and data export
- App Activity, Hosted MCPs, and Proxied MCPs (when enabled)
Can assign
Admin, Manager, Security, Developer, Analytics.
Manager
Role ID:
manager · Group: Admin · Scope: OrganizationCan access
- Invite, remove, and manage members
- Organization credentials
- Analytics, usage, and data export
Can assign
Analytics, Member.
Member
Role ID:
member · Group: Feature · Scope: Organization and Team · Baseline: YesCan access
- Create and use agents, skills, flowbooks, and custom operators
- Read organization metadata
- Create teams
- Manage personal credentials
- Leave the organization or a team
Can assign
Nothing.
Security
Role ID:
security · Group: Feature · Scope: Organization · Plan: EnterpriseCan access
- Custom Roles
- App Policies
- AI Model Access Controls
- App Activity, Hosted MCPs, and Proxied MCPs (on enabled orgs)
Can assign
Developer.
Developer
Role ID:
developer · Group: Feature · Scope: Organization · Requires: EnterpriseCan access
- Hosted MCPs and Proxied MCPs
- App Activity for their own servers and tools
- Standard content (agents, skills, flowbooks, custom operators) via Member
Can assign
Nothing.
Analytics
Role ID:
analytics · Group: Feature · Scope: Organization · Plan: EnterpriseCan access
- Organization analytics dashboard
- Usage limits and credit consumption
- Data export
Can assign
Nothing.
Team Roles
Teams use a simpler two-role system.Team Admin
Role ID:
admin (team scope) · Scope: TeamCan access
- All team content (agents, flowbooks, skills, custom operators)
- Team credentials
- Team analytics
- Team membership
Can assign
Team Admin, Team Member.
Team Member
Role ID:
member (team scope) · Scope: Team · Baseline: YesCan access
Read access to team content.
Can assign
Nothing.
Organization ceiling: org Admins hold
organization:manage_team_access, which lets them manage team memberships and team roles on every team in the organization, regardless of their team-level role. This is how org admins unblock access issues.Managing Roles
Roles are assigned and revoked individually from the Manage Roles sheet. You pick the exact combination of roles the user should hold. This is not a promote or demote action.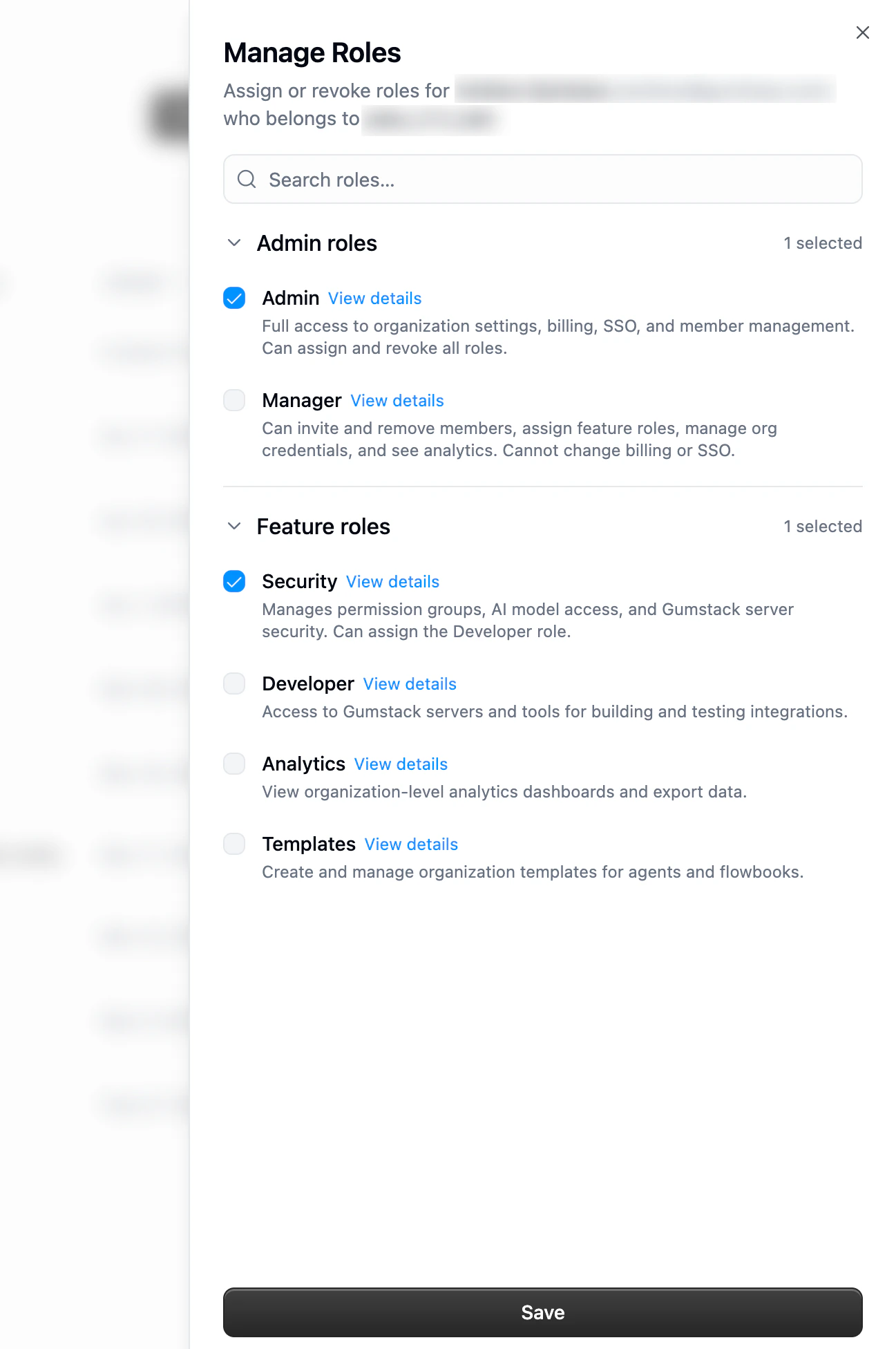
Open the members page
Go to Organization Members or a team’s Members tab.
Open Manage Roles
Click the three-dot menu next to the member and choose Manage Roles. The sheet opens with every role the member currently holds pre-selected.
Adding a new member with roles
Pre-assign organization roles when you invite someone so they land with the right permissions as soon as they accept.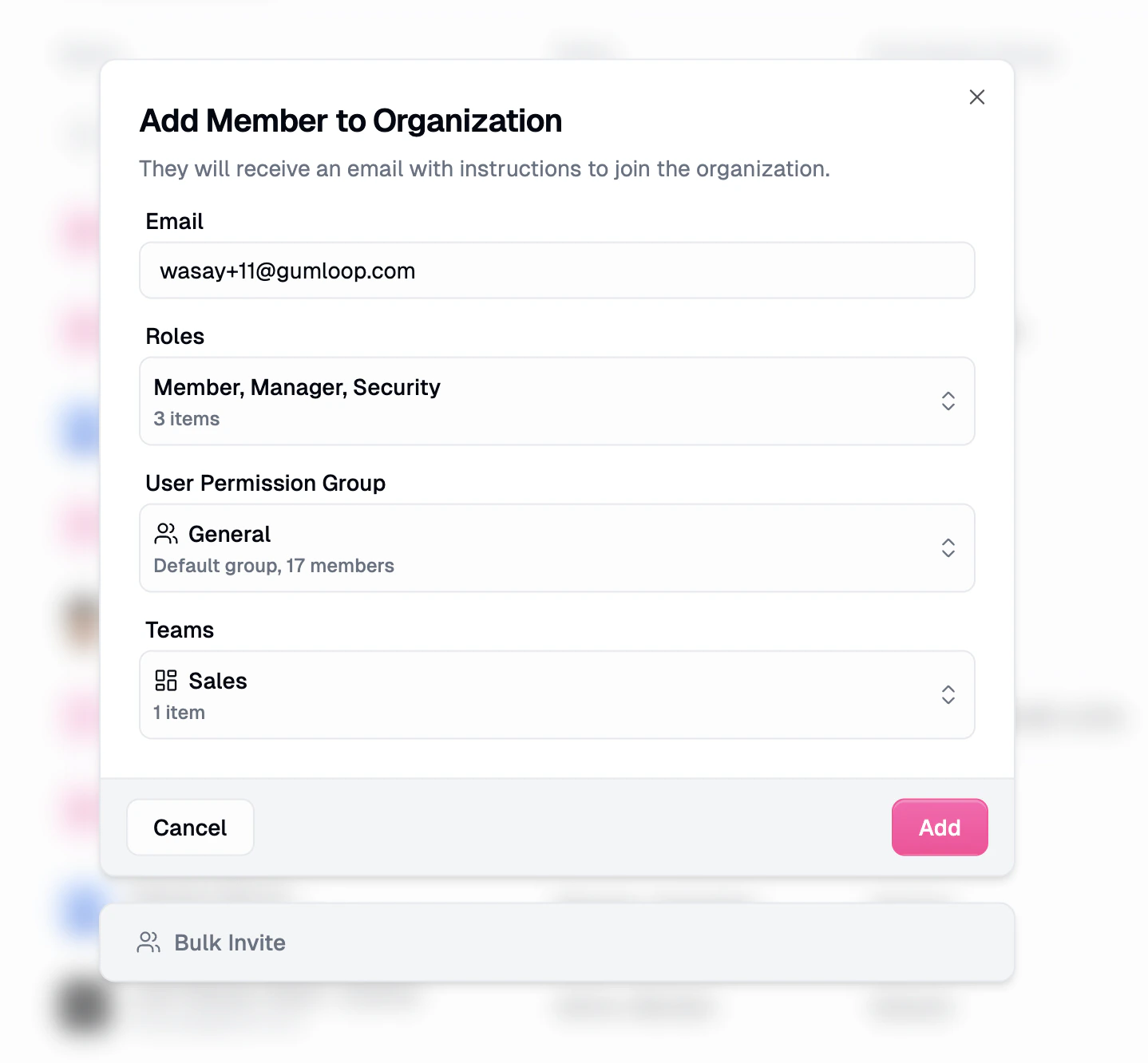
- Roles is a multi-select. Every invitee gets Member implicitly; pick any additional roles your own role lets you assign.
- Custom Roles picks one or more Custom Roles that apply subtractive restrictions on top of the organization roles. New invitees automatically join the default custom role; you can layer additional custom roles on top.
- Teams adds the invitee to one or more teams.
Best practices
Start minimal, then layer on
Start minimal, then layer on
Every user starts as Member automatically. Add the narrowest additional roles that match their responsibilities. You can always add more later.
Prefer feature roles over Manager or Admin
Prefer feature roles over Manager or Admin
If someone only needs analytics visibility, grant Analytics, not Manager. Keep the high-authority list short.
Use Security instead of Admin for guardrails
Use Security instead of Admin for guardrails
Custom roles, app policies, and AI model access no longer require Admin. Grant Security so platform and security teams can own guardrails without billing or SSO.
Review role assignments quarterly
Review role assignments quarterly
Additive roles make it easy to accumulate extras. Run a quarterly review and remove roles that are no longer needed.
How permissions resolve
When someone takes an action, Gumloop checks three things. The action goes through only if all three agree.1. Roles
The union of everything your organization and team roles grant at the relevant scope. This is the ceiling on what you can do.
2. Item sharing
For a specific agent, flowbook, or skill, the owner can grant you Editor, Viewer, or Use only. Sharing overrides the default per item.
3. Custom roles
Your Custom Roles can subtract from what roles and sharing allow. For example, they can block certain apps or nodes. A user can hold multiple custom roles, and the effective restriction is composed across all of them.
Role Comparison
Users with multiple roles get the union of the “Yes” columns.| Capability | Admin | Manager | Security | Developer | Analytics | Member |
|---|---|---|---|---|---|---|
| Billing and subscription | Yes | No | No | No | No | No |
| SSO / SAML / SCIM | Yes | No | No | No | No | No |
| Add and remove members | Yes | Yes | No | No | No | No |
| Assign roles | All | Analytics, Member | Developer | No | No | No |
| Audit logs | Yes | No | No | No | No | No |
| AI model access controls | Yes | No | Yes | No | No | No |
| App policies | Yes | No | Yes | No | No | No |
| Custom roles | Yes | No | Yes | No | No | No |
| Organization credentials | Yes | Yes | No | No | No | No |
| Org analytics, usage, data export | Yes | Yes | No | No | Yes | No |
| Create agents, skills, flowbooks, custom operators | Yes | Yes | Yes | Yes | Yes | Yes |
| Create teams | Yes | Yes | Yes | Yes | Yes | Yes |
| App Activity & MCP management (Enterprise) | Yes | No | Yes | Yes | No | No |
Related Resources
Custom Roles
Additive restriction roles that subtract from what organization roles grant.
App Policies
Allow or block specific apps for users.
AI Model Access Controls
Restrict which AI models users can call.
Audit Logging
Track every administrative action.
Teams
Group users and content for shared access.

